Azərbaycanda Onlayn Mərc Təhlükəsizliyi: Ödəniş, 2FA və Anti-Fırıldaq Metrikaları
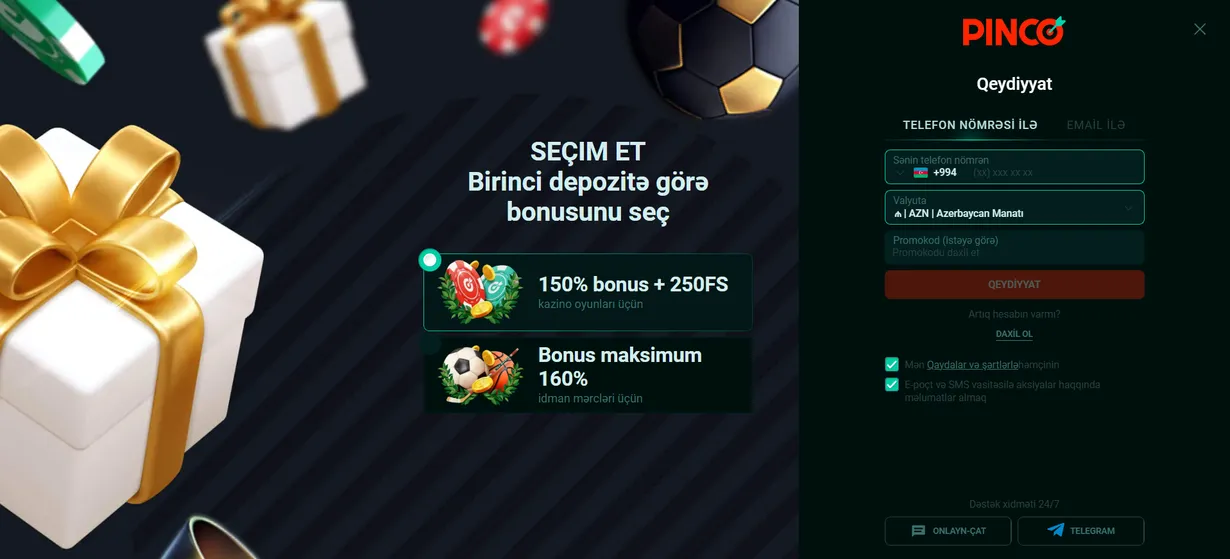
For users in Azerbaijan engaging with online platforms, understanding security and privacy is not optional-it’s essential. This guide explains the key terms and metrics you need to know to protect your personal information and financial assets like AZN. We will walk through payment security, two-factor authentication, anti-fraud systems, and common risks, providing a clear, step-by-step tutorial. For instance, a secure platform will never ask you to pinco yukle via an unverified third-party link. Let’s begin by breaking down the fundamental concepts.
Understanding Core Security Terminology
Before diving into settings, familiarize yourself with the language of digital security. These terms form the foundation of every safe online interaction.
- Two-Factor Authentication (2FA): A security process where you provide two different authentication factors to verify your identity, typically a password and a code sent to your phone.
- End-to-End Encryption (E2EE): A system of communication where only the communicating users can read the messages, preventing third-party access.
- SSL/TLS Certificate: A digital certificate that authenticates a website’s identity and enables an encrypted connection, indicated by ‘https://’ in the address bar.
- Anti-Fraud System: Software that uses algorithms and machine learning to detect and prevent suspicious or fraudulent transactions in real-time.
- KYC (Know Your Customer): A mandatory verification process where platforms confirm a user’s identity by requesting official documents like a passport or ID card.
- Data Privacy Policy: A legal document that explains how an organization collects, handles, and processes a user’s personal data.
- Payment Gateway: A merchant service that processes credit card or electronic payment transactions, acting as an intermediary between the user and the platform.
- Session Timeout: A security feature that automatically logs a user out after a period of inactivity to prevent unauthorized access.
- Cold Wallet: A method of storing cryptocurrency offline, making it inaccessible to online hacking attempts.
- Biometric Authentication: Using unique biological characteristics like fingerprints or facial recognition for identity verification.
Step-by-Step Guide to Payment Security
Your financial transactions are a primary target for cyber threats. Follow these steps to ensure your AZN deposits and withdrawals are secure.
Evaluating a Payment Method’s Safety
Not all payment options offer the same level of protection. Your choice should balance convenience with robust security features.
- Look for Localized Options: Prefer payment methods popular in Azerbaijan that are regulated and have a clear dispute resolution process.
- Check for Encryption: Ensure the payment page uses SSL encryption (look for the padlock icon in the browser).
- Use Dedicated Instruments: Consider using a pre-paid card or a separate bank account with a limited balance for online transactions to minimize risk.
- Verify Transaction Alerts: Activate SMS or email notifications for every transaction made from your card or e-wallet.
- Avoid Public Wi-Fi for Payments: Never conduct financial transactions over unsecured public networks.
- Review Statements Regularly: Scrutinize your bank and e-wallet statements weekly for any unauthorized charges.
Cryptocurrency Payment Precautions
While offering anonymity, cryptocurrencies require heightened personal security measures.
If you use Bitcoin or other cryptocurrencies, your security is entirely your responsibility. The platform does not control your private keys. Always transfer funds from your personal cold or hardware wallet to the platform’s provided address. Double-check the wallet address character-by-character before sending any funds, as crypto transactions are irreversible.
Implementing and Managing Two-Factor Authentication (2FA)
2FA is the single most effective step you can take to secure your account beyond a password. Here is how to set it up and manage it correctly.
- Access Security Settings: Log into your account and navigate to the ‘Security’ or ‘Account Settings’ section.
- Select 2FA Method: Choose between an authenticator app (like Google Authenticator or Authy) or SMS-based codes. Authenticator apps are generally more secure.
- Scan the QR Code: If using an app, open it and scan the QR code provided on the platform’s screen.
- Enter the Verification Code: The app will generate a 6-digit code. Enter this code on the platform to link your account.
- Save Backup Codes: The platform will provide a set of one-time-use backup codes. Store these in a secure, offline location.
- Test the Setup: Log out and log back in to ensure the 2FA process works smoothly.
Remember, if you lose access to your 2FA device and your backup codes, account recovery can be extremely difficult or impossible. Treat your backup codes with the same importance as your password.
How Anti-Fraud Systems Protect You
Modern platforms employ sophisticated anti-fraud systems that work behind the scenes. Understanding their metrics helps you see the protection in action.
| Metric / Signal | What It Monitors | Typical Action Taken |
|---|---|---|
| Velocity Checking | Number of transactions or login attempts per minute/hour. | Temporarily blocks the account or requires additional verification. |
| Geolocation Mismatch | Login from a new city/country shortly after a previous session. | Sends an alert email/SMS and may require 2FA. |
| Device Fingerprinting | Unique identifiers from your device (browser, OS, IP patterns). | Flags logins from unrecognized devices for review. |
| Transaction Pattern Analysis | Unusual deposit/withdrawal amounts compared to your history. | Delays the transaction for manual review by security staff. |
| Proxy/VPN Detection | Use of networks that hide your real IP address. | May restrict access or require identity confirmation. |
| Behavioral Biometrics | How you type, move your mouse, or hold your mobile device. | Can silently flag a session as high-risk for further monitoring. |
| Blacklist/IP Reputation | Connections from IP addresses known for malicious activity. | Blocks the connection attempt immediately. |
These systems are not infallible. Sometimes they may flag your legitimate activity. Cooperating with the platform’s verification requests is the fastest way to restore access. Qısa və neytral istinad üçün problem gambling helpline mənbəsinə baxın.
Common Privacy Risks and Mitigation Strategies
Beyond direct theft, your personal data has value. Protect your privacy with these proactive steps.
Data Collection and Usage
Platforms collect data for operational, security, and marketing purposes. Your goal is to understand and limit this where possible.
- Read the Privacy Policy: Skim the policy to understand what data is collected, how it’s stored, and if it’s shared with third parties.
- Limit Profile Information: Only provide information that is mandatory for KYC verification. Avoid adding unnecessary personal details in optional profile fields.
- Manage Communication Preferences: Opt out of promotional emails and newsletters if you do not wish to receive them.
- Use a Secure Email Address: Consider using a separate email account solely for your online platform registrations.
- Browser Hygiene: Regularly clear your browser cookies and cache, especially after using a public computer.
Phishing and Social Engineering Attacks
These attacks trick you into giving away your credentials or personal data voluntarily.
Be extremely wary of any communication-email, SMS, or social media message-that urges immediate action, such as “verify your account now” or “claim a bonus.” Legitimate platforms will never ask for your password or 2FA codes via these channels. Always navigate to the website directly by typing the URL yourself, rather than clicking on links in messages. Mövzu üzrə ümumi kontekst üçün 2FA basics mənbəsinə baxa bilərsiniz.
The Regulatory Context in Azerbaijan
Understanding the local legal landscape is crucial for assessing a platform’s commitment to security and privacy.
Currently, the regulation of online platforms in Azerbaijan is evolving. This places a greater responsibility on the user to perform due diligence. A platform operating with a strong security posture will often hold an international license from a reputable jurisdiction (like Malta, Curacao, or the UK), which mandates strict data protection standards, fair play certification, and responsible gambling tools. Look for evidence of these licenses and certifications in the website footer, as they imply adherence to external audits and security protocols that protect user data and funds.
Creating Your Personal Security Checklist
Combine all the knowledge into a routine. Perform these checks regularly to maintain your security hygiene.
- Password Audit: Change your password every 90 days. Use a unique, complex password not used elsewhere.
- 2FA Status: Confirm your 2FA is active and your backup codes are accessible.
- Linked Payment Methods: Review and remove any saved payment methods you no longer use.
- Active Sessions: Check your account for a “Active Sessions” log and log out from any unfamiliar devices or locations.
- Document Expiry: If you completed KYC, note when your submitted ID document expires to avoid verification delays later.
- Software Updates: Ensure your device’s operating system, browser, and antivirus software are up-to-date.
Security is not a one-time setup but an ongoing practice. By internalizing these terms, metrics, and steps, you build a strong personal framework that safeguards your online activity, allowing you to focus on your experience with greater confidence and control. Your awareness is the most effective security tool available.
